Compliance Assistant
- Latest Dynatrace
- App
- 3-min read
 Compliance Assistant supports and helps you to:
Compliance Assistant supports and helps you to:
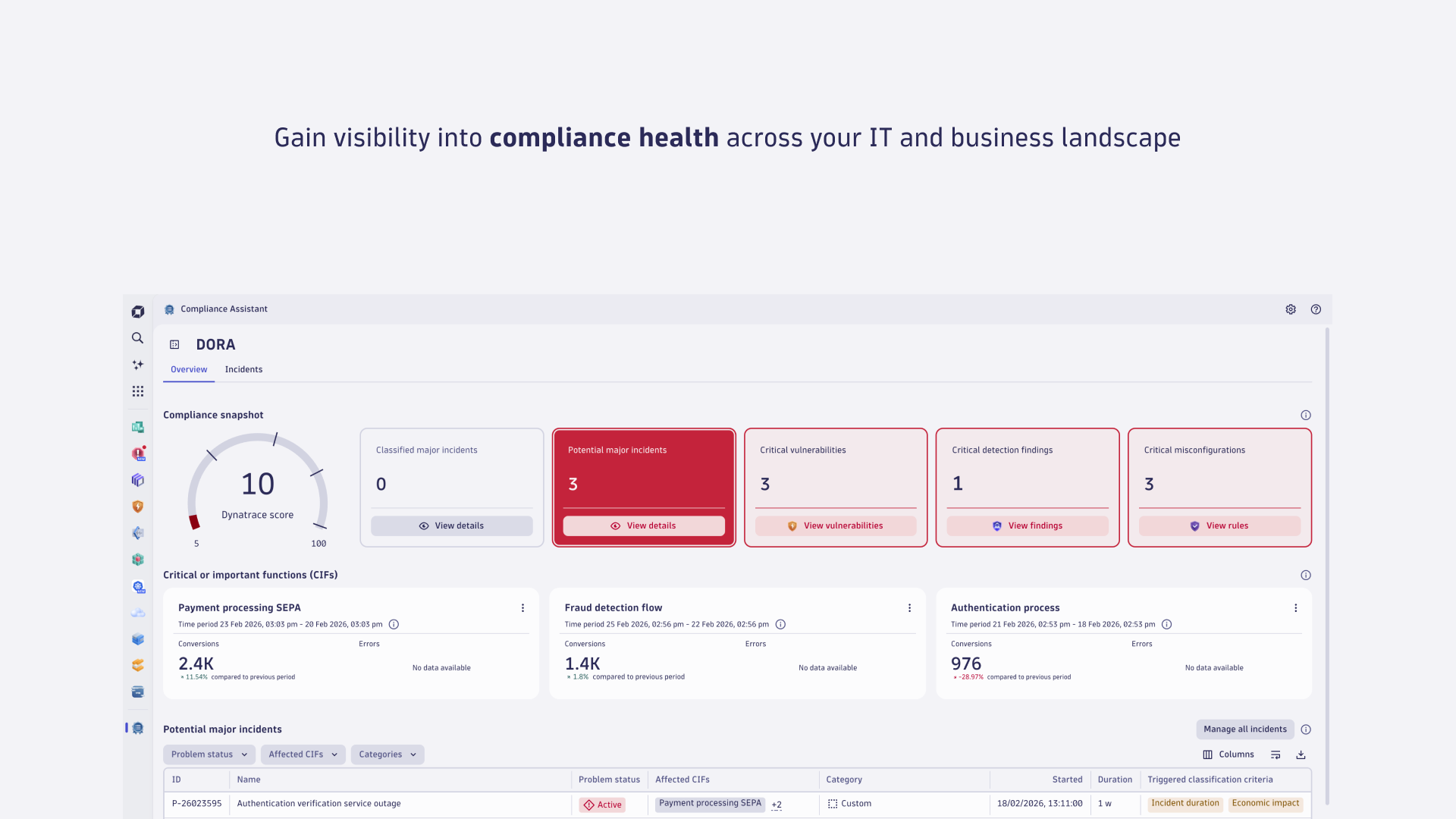
- Track, manage, and automate compliance across your IT and business landscape.
- Gain real-time visibility into compliance risks with regulations and certifications out-of-the-box.
- Monitor compliance health across critical business processes to ensure continuous monitoring and automating incident classification.
Prerequisites
Installation
Make sure the app is installed in your environment.
Permissions
The following table describes the required permissions.
Set up sources and applications
To take full advantage of  Compliance Assistant, get started with
Compliance Assistant, get started with  Business Flow to monitor and analyze compliance-critical business processes.
Business Flow to monitor and analyze compliance-critical business processes.
To maximize the value of risk management insights, set up data sources for security events from your monitored environment or from third-party sources. Security-related data includes vulnerability events, compliance events, and detection finding events.
Get started
 Compliance Assistant offers monitoring and automation capabilities streamlined to specific compliance frameworks. To start managing compliance, set up a compliance framework applicable to your organization.
Compliance Assistant offers monitoring and automation capabilities streamlined to specific compliance frameworks. To start managing compliance, set up a compliance framework applicable to your organization.
Set up a compliance framework
- In Dynatrace, go to
 Compliance Assistant.
Compliance Assistant. - Select Set up framework.
- To choose the compliance framework you want to monitor, select the relevant framework. Currently, DORA is the only available framework in
 Compliance Assistant.
Compliance Assistant. - Select Next.
- To select critical or important functions (CIFs), select all compliance-critical business processes. If no CIFs are available, create a new business process with configuration as an entity in
 Business Flow.
Business Flow. - Select Next.
- To take full advantage of the ICT risk management capabilities, verify whether data sources for security events are properly configured in your environment.
If vulnerabilities aren't enabled
- Select Set up RVA to go to Vulnerability Analytics: General settings and enable Runtime Vulnerabilities Analytics. There are two tabs: Third-party Vulnerability Analytics and Code-level Vulnerability Analytics. You can enable one or more options there.
- To monitor third-party vulnerabilities, enable third-party vulnerability detection.
- To monitor code-level vulnerabilities, enable code-level vulnerability detection.
- To integrate external security data into Grail, you can ingest vulnerability events from third-party products. For a list of supported integrations, see Security integrations.
- Select Done.
If security detection findings aren't enabled
- Select Set up RAP to go to
 Settings > Analyze and alert > Application security > Application protection and enable Runtime Application Protection.
Settings > Analyze and alert > Application security > Application protection and enable Runtime Application Protection. - To integrate external security data into Grail, you can ingest detection finding events from third-party products. For a list of supported integrations, see Security integrations.
- Select Done.
If ICT asset configuration rules aren't enabled
- Select Set up KSPM to go to Security Posture Management: Kubernetes and enable Security Posture Management.
- To get started with Security Posture Management and configure the assessment scope, see Get started with Security Posture Management. To include DORA as a supported compliance standard in the assessment scope, go to
 Settings > Analyze and alert > Application security > Security Posture Management and enable DORA.
Settings > Analyze and alert > Application security > Security Posture Management and enable DORA. - To integrate with external security data to ingest compliance findings, see Security integrations.
- Select Done.
Remove a compliance framework
- Go to
 Settings > Apps >
Settings > Apps >  Compliance Assistant.
Compliance Assistant. - Under the relevant compliance framework, such as DORA, select Remove framework.
- Select Remove to confirm. Be aware that removing a compliance framework impacts all
 Compliance Assistant users.
Compliance Assistant users.
Manage compliance-critical business processes
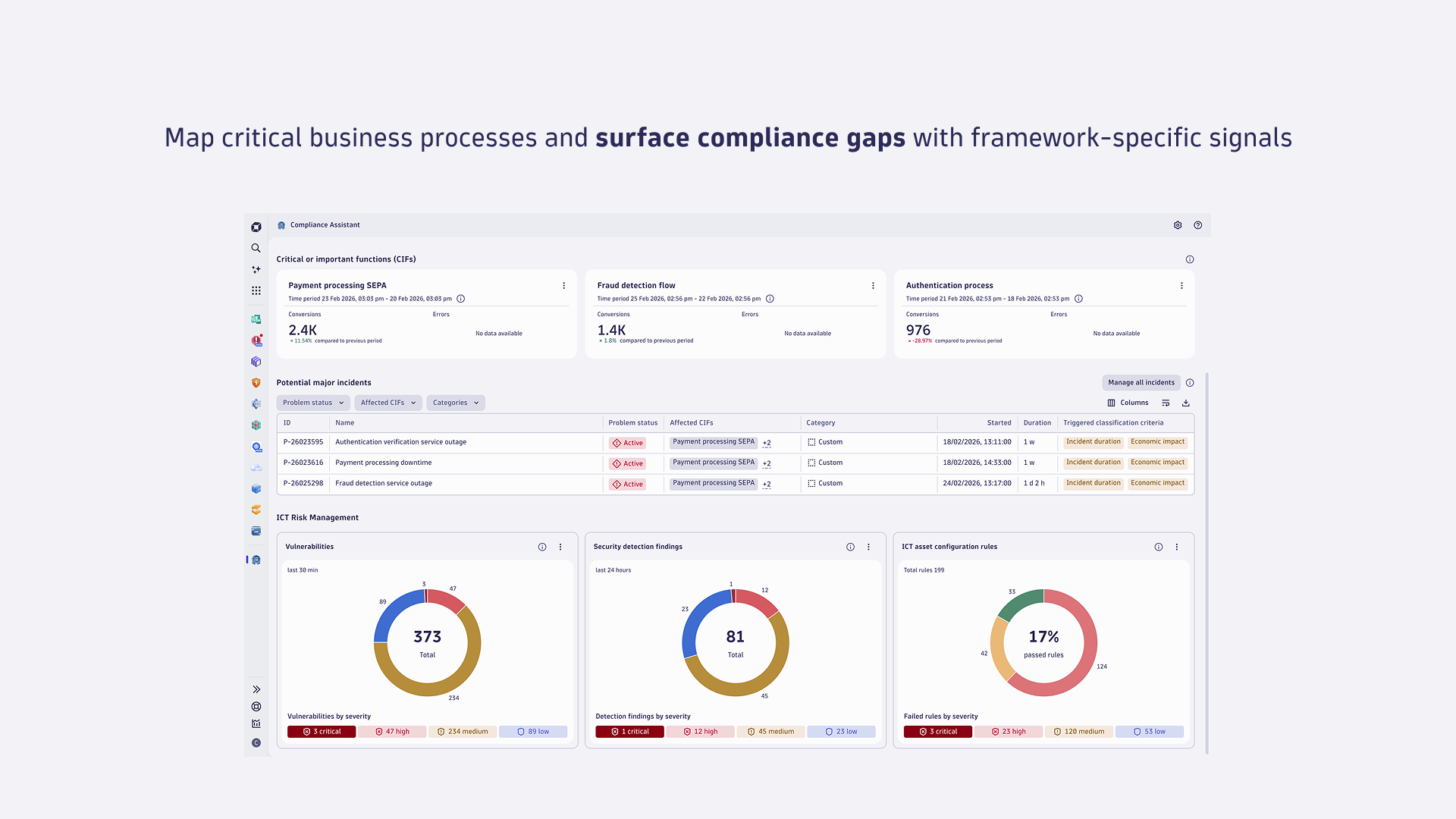
 Compliance Assistant allows you to map compliance-relevant IT assets to end-to-end business processes.
Compliance Assistant allows you to map compliance-relevant IT assets to end-to-end business processes.  Compliance Assistant integrates with
Compliance Assistant integrates with  Business Flow to identify compliance-critical business process with configuration as an entity.
Business Flow to identify compliance-critical business process with configuration as an entity.
To add a critical or important function (CIF)
- Go to
 Settings > Apps >
Settings > Apps >  Compliance Assistant.
Compliance Assistant. - Under the compliance framework DORA, select Add CIFs.
- From the table, select business processes to add as CIFs.
- Select Save to update the compliance framework.
To remove a critical or important function (CIF)
- Go to
 Settings > Apps >
Settings > Apps >  Compliance Assistant.
Compliance Assistant. - Under the compliance framework DORA, select the menu icon of the CIF to remove.
- From the menu, select Remove CIF.
- Select Remove to confirm. Be aware that removing a CIF impacts all
 Compliance Assistant users.
Compliance Assistant users.
To edit the estimated cost per minute of an incident
- Go to
 Settings > Apps >
Settings > Apps >  Compliance Assistant.
Compliance Assistant. - Under the compliance framework DORA, select the menu icon of the relevant CIF.
- From the menu, select Edit incident cost/min.
- Add the estimated incident cost per minute to be used to calculate the economic impact of incidents impacting specific CIF.
- Select Save.
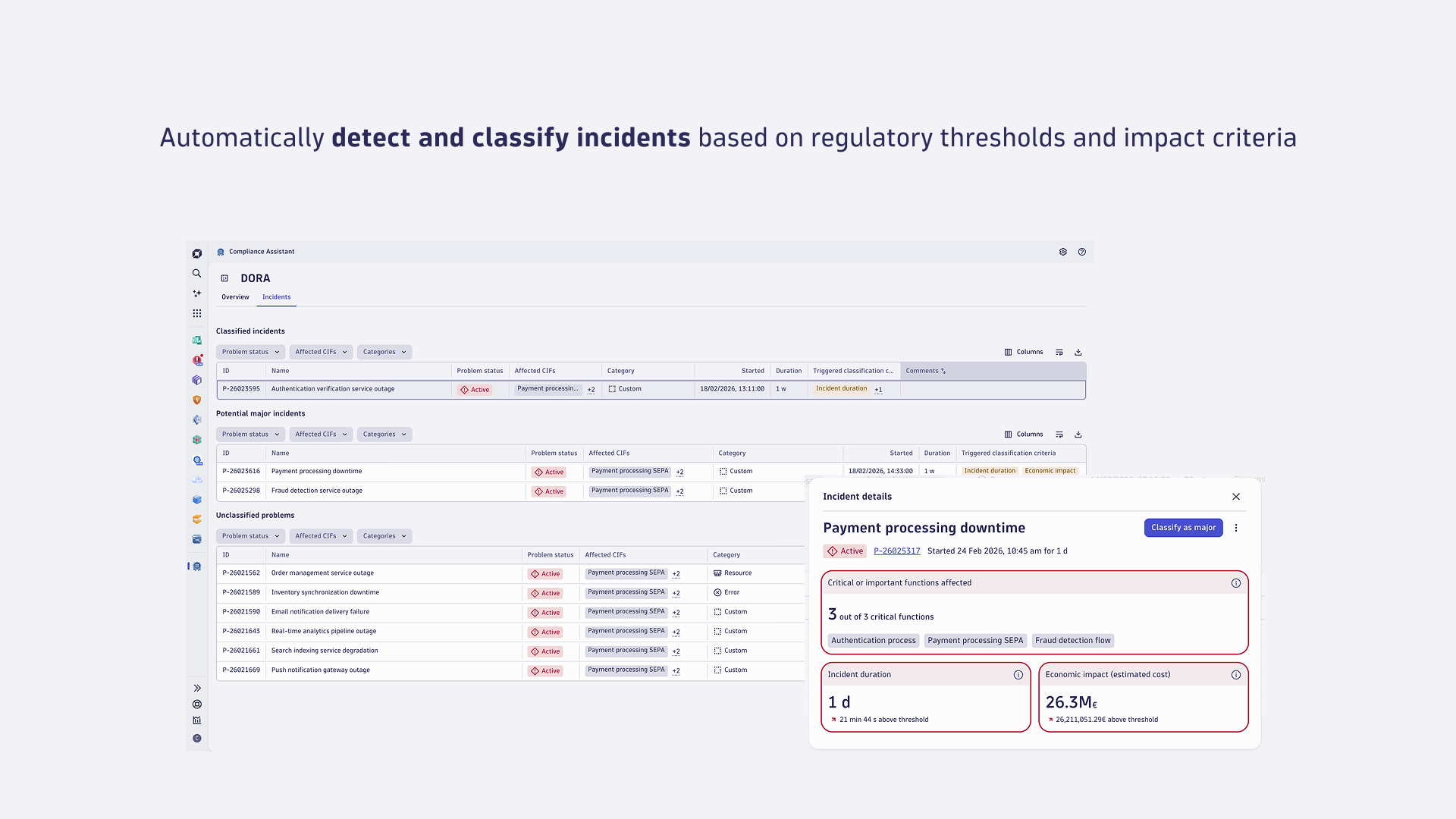
Manage compliance incidents
 Compliance Assistant
Compliance Assistant
- Is designed to help you manage incidents in line with compliance requirements.
- Automatically classifies incidents based on regulatory impact thresholds and accelerates reporting of major incidents to align with regulatory deadlines.
- Streamlines the assessment of IT-detected incidents affecting business processes configured as CIFs into unclassified problems, potential major incidents, and classified major incidents.
To investigate and classify potential compliance incidents
- Go to
 Compliance Assistant.
Compliance Assistant. - See the Incidents section for tables of potential major incidents and unclassified problems.
- Select the relevant incident to view the following details on any triggered classification threshold according to the EU DORA Regulation:
- Critical or important functions (CIFs) affected by the incident.
- Incident duration, calculated on the basis of the duration of the underlying problem in nanoseconds. The materiality threshold for the classification criterion is met when the duration of the incident is longer than 24 hours (RTS on the classification of ICT-related incidents and cyber threats).
- The economic impact of the incident is calculated on the basis of the estimated incurred cost per minute of the affected CIFs and the duration of the underlying problem. To learn more about configuring the estimated cost value per minute, see Edit the estimated cost per minute of an incident. The materiality threshold for the classification criterion
Economic impactis met where the costs and losses incurred by the financial entity due to the incident have exceeded or are likely to exceed €100,000 (RTS on the classification of ICT-related incidents and cyber threats).
- To classify an incident as major in line with EU DORA, from the incident details view, select Classify as major.
- Optional: Add a comment to document your decision. This comment is added to the incident classification business event.
- Select Confirm.
- Be aware that classification triggers ingestion of a business event with the details of the classified compliance incident and the process may take a few seconds.
- The classified incident is now available in
 Compliance Assistant > Incidents > Classified incidents.
Compliance Assistant > Incidents > Classified incidents.
Concepts
Compliance framework
A compliance framework is a structured set of requirements, guidelines, and best practices to support organizations in meeting regulatory and industry-specific standards.
 Compliance Assistant consolidates insights and functionalities tailored to a specific compliance framework.
Compliance Assistant consolidates insights and functionalities tailored to a specific compliance framework.  Compliance Assistant currently offers monitoring and automation capabilities supporting compliance with the EU DORA Regulation.
Compliance Assistant currently offers monitoring and automation capabilities supporting compliance with the EU DORA Regulation.
Dynatrace score in compliance snapshot
A real-time, tiered score summarizing your current ICT risk posture across potential incidents, security detection findings, vulnerabilities, and misconfigurations. This score is an indicative metric based on current data and tier logic. This score is a high-level indicator based on real-time observability and automated systems. It does not replace comprehensive or formal compliance assessments.
Critical or important functions (CIFs)
According to the EU DORA Regulation, financial entities must identify, classify, and document ICT-supported business functions and their supporting assets. CIFs are processeses that, if disrupted, could significantly impact financial performance or service continuity.
 Compliance Assistant allows you to map compliance-relevant IT assets to end-to-end business processes. By integrating with
Compliance Assistant allows you to map compliance-relevant IT assets to end-to-end business processes. By integrating with  Business Flow, you can identify compliance-critical business processes, leveraging Smartscape entities for enhanced visibility and context.
Business Flow, you can identify compliance-critical business processes, leveraging Smartscape entities for enhanced visibility and context.
Unclassified problems
IT-detected incidents are affecting any of the business processes configured as CIFs that  Business Flow is monitoring. Incidents are considered unclassified problems when less than one of the materiality thresholds for the classification of major incidents is breached. In line with the EU DORA Regulation, it must be assessed whether an incident affects or has affected ICT services or network and information systems that support CIFs (RTS on the classification of ICT-related incidents and cyber threats).
Business Flow is monitoring. Incidents are considered unclassified problems when less than one of the materiality thresholds for the classification of major incidents is breached. In line with the EU DORA Regulation, it must be assessed whether an incident affects or has affected ICT services or network and information systems that support CIFs (RTS on the classification of ICT-related incidents and cyber threats).
Potential major incidents
IT-detected incidents are affecting any of the business processes configured as CIFs that  Business Flow is monitoring. Incidents are considered potential major incidents when two or more of the monitored materiality thresholds for the classification of major incidents are breached. In line with the EU DORA Regulation, an incident is considered major when two or more of the materiality thresholds are met (RTS on the classification of ICT-related incidents and cyber threats).
Business Flow is monitoring. Incidents are considered potential major incidents when two or more of the monitored materiality thresholds for the classification of major incidents are breached. In line with the EU DORA Regulation, an incident is considered major when two or more of the materiality thresholds are met (RTS on the classification of ICT-related incidents and cyber threats).
Classified major incidents
IT-detected incidents are affecting any of the business processes configured as CIFs that  Business Flow is monitoring and have been manually classified as major in line with the EU DORA Regulation. Once an incident is classified as major, Dynatrace automatically generates a business event with a snapshot of the compliance incident. Learn more about Compliance incident classification events.
Business Flow is monitoring and have been manually classified as major in line with the EU DORA Regulation. Once an incident is classified as major, Dynatrace automatically generates a business event with a snapshot of the compliance incident. Learn more about Compliance incident classification events.
Vulnerabilities
 Compliance Assistant relies on vulnerability findings to proactively mitigate risks before they escalate into incidents. In line with the EU DORA Regulation, organizations are required to assess vulnerabilities on a continuous basis. A vulnerability finding is a security event that highlights a detected weakness in a system, software component, or environment.
Compliance Assistant relies on vulnerability findings to proactively mitigate risks before they escalate into incidents. In line with the EU DORA Regulation, organizations are required to assess vulnerabilities on a continuous basis. A vulnerability finding is a security event that highlights a detected weakness in a system, software component, or environment.
Security detection findings
 Compliance Assistant relies on detection finding events to support in prioritizing cyber risks. In line with the EU DORA Regulation, organizations are required to assess cyber threats on a continuous basis (RTS on ICT risk management framework). A detection finding event is generated when suspicious activity is observed around an object.
Compliance Assistant relies on detection finding events to support in prioritizing cyber risks. In line with the EU DORA Regulation, organizations are required to assess cyber threats on a continuous basis (RTS on ICT risk management framework). A detection finding event is generated when suspicious activity is observed around an object.
ICT asset configuration results
 Compliance Assistant relies on compliance events to detect potential misconfigurations. In line with the EU DORA Regulation, organizations are required to identify a secure configuration baseline for ICT assets that minimizes exposure to cyber threats and regularly verify that those baselines are effectively deployed (RTS on ICT risk management framework). Compliance events represent the assessment of a resource in the context of the rule specified in the compliance standard.
Compliance Assistant relies on compliance events to detect potential misconfigurations. In line with the EU DORA Regulation, organizations are required to identify a secure configuration baseline for ICT assets that minimizes exposure to cyber threats and regularly verify that those baselines are effectively deployed (RTS on ICT risk management framework). Compliance events represent the assessment of a resource in the context of the rule specified in the compliance standard.
Use cases
Compliance Assistant enables you to achieve and manage compliance across supported frameworks:
- Identify and map compliance-relevant IT assets by analyzing critical end-to-end business processes — promoting cross-functional alignment between IT, security, and business teams.
- Continuously track compliance status against a selected framework and detect risks using real-time data on vulnerabilities, detection findings, and misconfigurations.
- Detect, classify, and accelerate reporting of incidents that meet regulatory thresholds, automating the steps needed to comply with tight regulatory deadlines.
FAQ
How can I improve the Dynatrace score in the compliance snapshot?
The Dynatrace score is a real-time indicator based on your current ICT risk posture and impacted by the severity of findings. To improve your score:
- Address potential major incidents and unclassified problems promptly.
- Remediate security detection findings and vulnerabilities. To review security detection findings and initiate deeper analysis, see Gain insights. To learn more on how to fix detected vulnerabilities, see How do I fix detected vulnerabilities?.
- Fix ICT asset misconfigurations identified by Security Posture Management. For guidelines on how to fix findings, see Stay compliant with Security Posture Management.
- Ensure proper monitoring and real-time protection are enabled across your critical or important functions (CIFs).
How often are insights on critical or important functions (CIFs) updated in  Compliance Assistant?
Compliance Assistant?
Insights on conversions and errors KPIs on CIFs are updated on the basis of the configured generation frequency of the KPI monitoring in  Business Flow. The evaluation timeframe for the monitored KPIs of critical or important functions (CIFs) is also defined in setting up a business configuration as an entity.
Business Flow. The evaluation timeframe for the monitored KPIs of critical or important functions (CIFs) is also defined in setting up a business configuration as an entity.
To ensure reliable KPI evaluation and avoid missing data from long‑running processes, set the evaluation timeframe to at least three to four times the process's average duration (for example, if the average duration of the CIF is 5 minutes, set the window to at least 15–20 minutes).
Why are the configured critical or important functions (CIFs) not updating?
If you have recently edited or added business processes configured as entity and selected any of those as a CIF in  Compliance Assistant, it may take up to the maximum defined frequency for the monitoring KPIs of those business processes to be updated in
Compliance Assistant, it may take up to the maximum defined frequency for the monitoring KPIs of those business processes to be updated in  Compliance Assistant. You can adjust the monitoring frequency in the business flow configuration.
Compliance Assistant. You can adjust the monitoring frequency in the business flow configuration.
 Compliance Assistant (Preview)
Compliance Assistant (Preview)